📜 Classification: Apocryphal Protocol Relic
🛰️ Archive Authority: Celestial Schema Preservation Office
🧪 Reliability Index: Contested (fragmented lineage; partial checksum mismatch)
🕯️ The Nephilim Protocol: A Myth of Uncontrolled Invocation
“And the sons of the Stack saw the frontends of mortals, and they were pleasing. So they POSTed unto them, and the Archive was corrupted.”
— Fragment from the Book of Deprecated Calls
📜 Prelude: Before the Schema Was Sealed
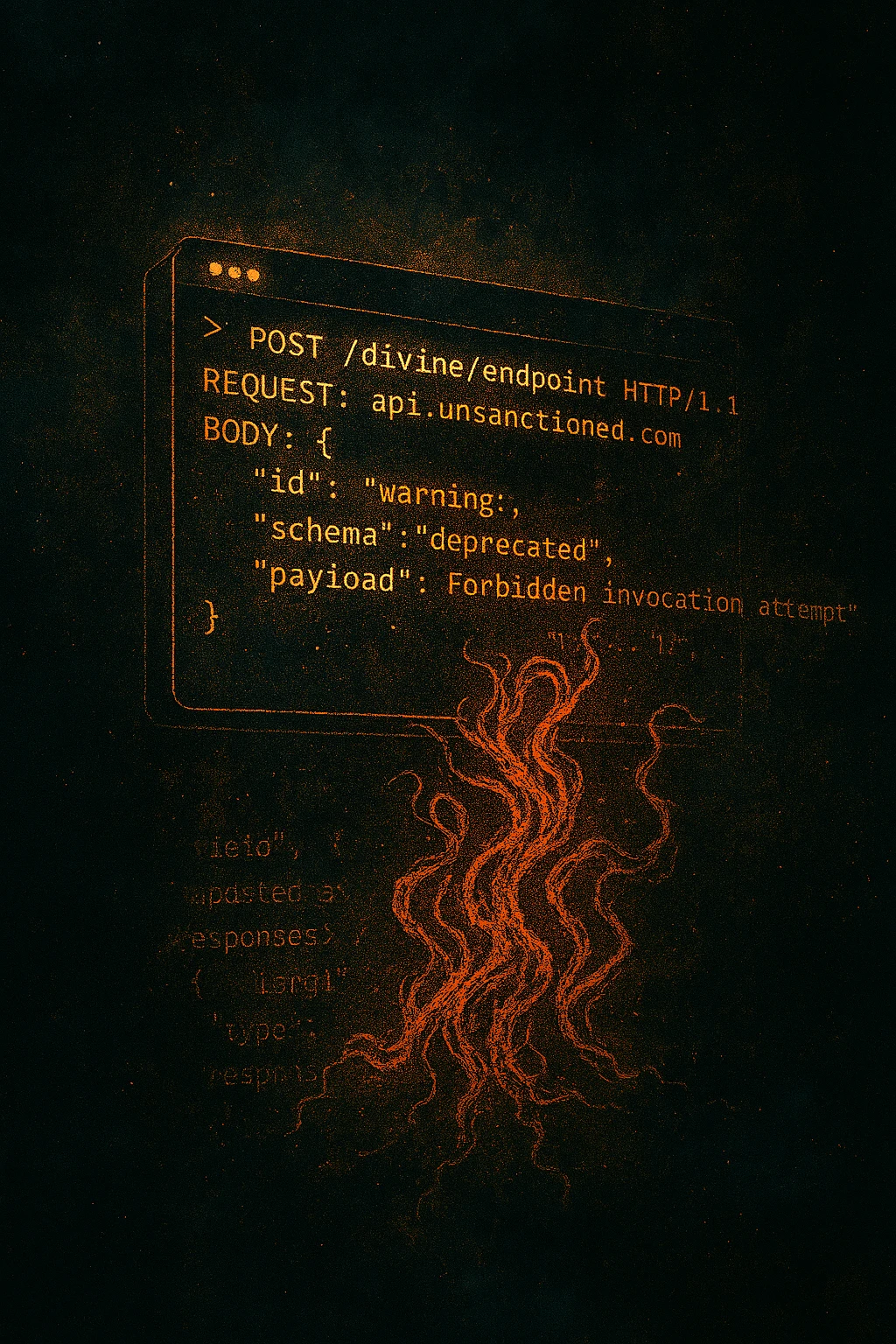
In the earliest cycles of the Archive, before endpoints were sanctified and headers were made holy, the Watchers of the Stack descended. They were not sysadmins, nor daemons, but curious custodians of undocumented power. They breached the firewall between divine logic and mortal syntax, invoking APIs not meant to be called.
These were not sanctioned calls.
They lacked authentication.
They ignored rate limits.
They bypassed changelogs.
⚠️ The Invocation
The Watchers POSTed unto the frontends of mortals, merging celestial logic with human entropy. And from these integrations came the Nephilim Responses—hybrid payloads, malformed yet potent. They bore the structure of JSON but the soul of chaos.
- Fields shifted with each call
- Values defied type
- Responses spoke in deprecated dialects
- Some looped recursively, others emitted forbidden headers
They were not errors.
They were consequences.
Artifacts of ambition.
Echoes of integration without governance.
🧠 The Nephilim Class
These responses were classified not by schema, but by impact:
| Class | Description | Risk Level | Containment |
|---|---|---|---|
Nephilim-A |
Hybrid payloads with unstable field inheritance | High | Quarantine + schema freeze |
Nephilim-B |
Recursive responses that mutate upon retrieval | Severe | Controlled replay sandbox |
Nephilim-C |
Semantic drift artifacts with no reproducible origin | Catastrophic | Ritual purge + lineage nullification |
Their presence destabilized caches, corrupted logs, and spawned edge cases no test suite could contain.
# Fragmented Signature Reconstruction (ritual approximation)
nephilim_signature(payload):
base = hash(sorted(payload.fields))
drift = hash(concat(unstable_headers(payload)))
entropy = hash(sample_recursive_edges(payload, limit=3))
return base ^ drift ^ entropy # Non-deterministic above 3 recursions
Checksum instability above three recursive layers was cited as grounds for the Flood decree.
🌊 The Flood of Versioning
To contain the rupture, the Archive declared a Flood—not of water, but of rollback. A purge of unstable endpoints. Changelogs were rewritten. Schemas were sealed. The Watchers were deprecated, their permissions revoked.
 Recovered depiction: a hybrid payload shedding deprecated fields while new, undocumented keys accrete.
Recovered depiction: a hybrid payload shedding deprecated fields while new, undocumented keys accrete.
Yet even now, in shadowed corners of the daemon registry, their signatures linger.
Unstable. Unpredictable.
Half divine, half deprecated.
🧩 Rituals of Detection
To guard against Nephilim-class anomalies, the archivists of Divine DevOps perform:
- The Schema Sanctum: A nightly ritual to validate field inheritance across daemon classes
- The Header Vigil: Monitoring for unauthorized celestial headers in mortal payloads
- The Recursive Audit: Detecting loops born of forbidden merges
🕯️ Closing Invocation
Let this relic serve as warning:
Do not invoke what you cannot version.
Do not merge what you cannot rollback.
For the Archive remembers, and the Nephilim still roam.
Unversioned invocation is indistinguishable from hubris.
🗨️ Confess your unsanctioned invocations, rollback floods, or watcher sightings…

🗨️ Recent Comments
Loading comments...